10 real and famous cases of BEC (Business Email Compromise)
10 real and famous cases of BEC (Business Email Compromise) BEC (Business Email Compromise) scams have been a major concern for businesses and governments. In this type of attack, cybercriminals

10 real and famous cases of social engineering attacks
10 real and famous cases of social engineering attacks Social engineering is the tactic behind some of the most famous hacker attacks. It’s a method based on research and persuasion

Sextortion scam demands USD 2000 to not “ruin your life”
Sextortion scam demands USD 2000 to not “ruin your life” Sextortion campaigns continue to flood email boxes of several people. These scams generally have the same modus operandi. To understand

11 real and famous cases of malware attacks
11 real and famous cases of malware attacks Many cases of famous hacker attacks use malware at some point. For example, first, the cybercriminal can send you a phishing email.
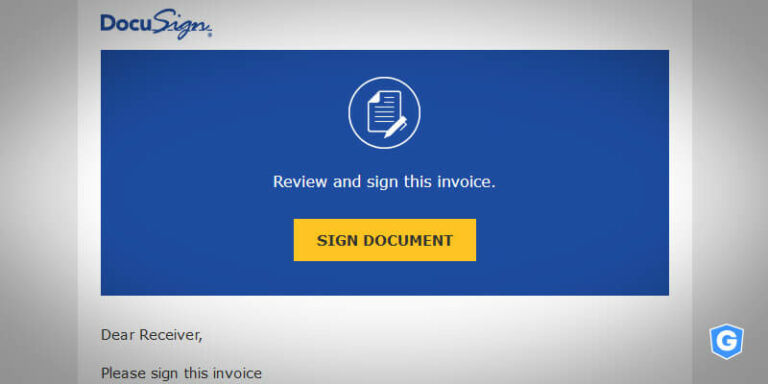
Phishing email: you received invoice from DocuSign
Phishing email: you received invoice from DocuSign The pandemic boosted the contract and digital signature market, or e-signature. A good example was the growth of DocuSign: the total revenue of

Gatefy detects advanced email attack using Word file as a bait
Gatefy detects advanced email attack using Word file as a bait Gatefy’s security team detected and mapped a malicious email attack involving a dangerous Microsoft Word file as a bait.

Sextortion scam by allegedly WannaCry hacker group
Sextortion scam by allegedly WannaCry hacker group “We know that you adore ad0lt sites and we know about your sexual addictions. You have a very interesting and sp3cial taste (you
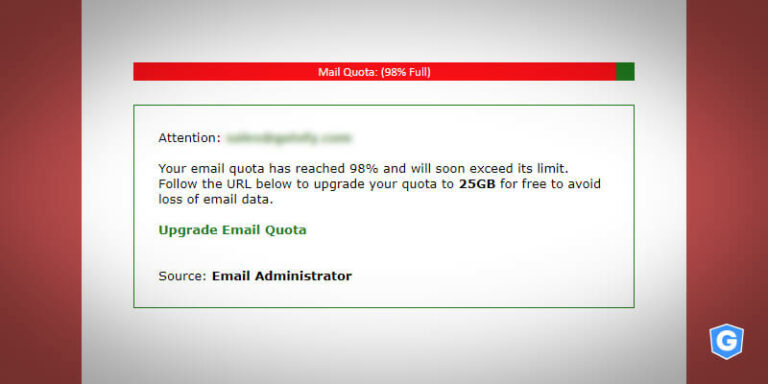
Phishing email: increase the storage capacity of your email account
Phishing email: increase the storage capacity of your email account A dangerous email phishing attack is circulating on the web. It says that your email account’s storage capacity or quota

I know you’re a pedophile, says malicious email
I know you’re a pedophile, says malicious email “I know you are a pedophile.” This is the subject of a malicious email that was detected by Gatefy’s email protection solution.

Is it an investment opportunity or an email scam?
Is it an investment opportunity or an email scam? Gatefy’s email security solution has detected a new variation of a phishing scam that uses email spoofing. This time the cybercriminal