
Less than 10 minutes for an 11-year-old boy to hack an election results website
Less than 10 minutes for an 11-year-old boy to hack an election results website Less than 10 minutes was the time an 11-year-old boy took to hack a replica of

Social engineering: what it is and how it works
Social engineering: what it is and how it works The following question will help you understand the term social engineering: Is it easier, in general, to persuade, lie and manipulate

Phishing scam connects you to a fake Apple support
Phishing scam connects you to a fake Apple support Apple users with iCloud accounts are being targeted on a new phishing attack. They receive emails saying that there were problems

Agency in UK warns about phishing campaigns
Agency in UK warns about phishing campaigns “The NCSC is investigating a large-scale phishing campaign affecting sectors including transport, engineering and defence”. This is how one of the recent NCSC

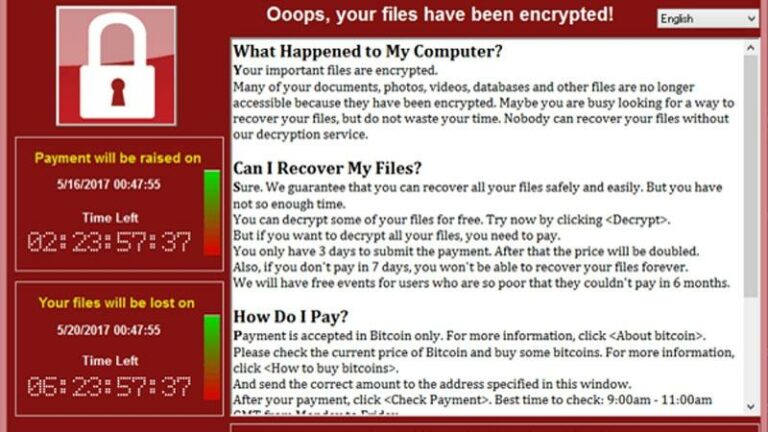
Got infected with ransomware? Check out what to do
Got infected with ransomware? Check out what to do If your device shows you a message such as: “Ooops, your files have been encrypted”; or “Your files will be lost
How to prevent a ransomware attack
How to prevent a ransomware attack Ransomwares will continue for a long time to be one of the biggest threats in the virtual world. The good news is that there

Understanding Zero-Day Exploit and Zero-Day Vulnerability
Understanding Zero-Day Exploit and Zero-Day Vulnerability It’s quite common to see the terms Zero-Day Exploit, Zero-Day Attack, and Zero-Day Vulnerability on news websites and cybersecurity solutions vendors. But what do
Fake WannaCry emails still in action
Fake WannaCry emails still in action Remember WannaCry? This name continues to cause a lot of panic around the world. We know that there is a very strong reason for

Sandbox or Content Disarm & Reconstruction (CDR)?
Sandbox or Content Disarm & Reconstruction (CDR)? We are here today to help you answer the following question: Should I invest in a Sandbox or CDR solution? This is a

8 tips to manage and improve your business’s cybersecurity
8 tips to manage and improve your business’s cybersecurity With so many attacks and data breaches making the headlines in the past few years, it’s easy for anyone to see